About
A SSL/TLS session is a session between two applications that have successfully performed an SSL Handshake.
Management
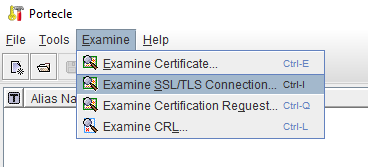
Test the connection and see the server certificates
You can examine the connection and server certificate connection with portecle
See the session info
With OpenSsl and the s_client command 1)
openssl s_client -connect host:443 -state -debug
At the end of the handshake, you can see the session info.
SSL-Session:
Protocol : TLSv1.3
Cipher : TLS_AES_256_GCM_SHA384
Session-ID: 38E38C70E914EA40D81C47E662EE477109A79F93362EB0BA9D7DB9BEF9F79A02
Session-ID-ctx:
Resumption PSK: 7A877BEAA39FC03077ACAC5D8F875E0D9C3942E9EC17FDEA19255AFCD8CC697323C217FF4AF6EAB65123FED80457D42E
PSK identity: None
PSK identity hint: None
SRP username: None
TLS session ticket lifetime hint: 14400 (seconds)
TLS session ticket:
0000 - 47 ea 4d 76 24 fa a9 01-08 85 5a 02 e2 f2 14 60 G.Mv$.....Z....`
0010 - 6a 51 cc e1 90 65 0c 22-6c 6b 0e 48 34 c0 34 5e jQ...e."lk.H4.4^
Start Time: 1647165467
Timeout : 7200 (sec)
Verify return code: 0 (ok)
Extended master secret: no
Max Early Data: 0