How to enable SSL on a server (ie HTTPS on a web server) ?
About
This page shows you how to enable SSL for a server (ie service).
This is how you enable HTTPS (HTTP over SSL) for a web server.
What do I need to configure?
In order to enable SSL, you need to add:
- a certificate:
- and the corresponding private key
You need one pair
- by hostname
- or by apex domain with a wildcard certificate
Why?
Because when an application (for instance a browser) connects to a server (for instance a web server), it can:
- initiate the SSL handshake
This certificate usage is also known as the SSL/TLS Web Server Authentication or server authentication for short.
In the handshake, the client can also authenticate itself to the server if it presents its certificat known as the client certificate but this is optional.
Component
To enable ssl (https) on a server, you need:
-
- It's a private entity and should not be shared (only the owner should have access)
- However, it must be readable by the web server process in order to:
- create and send the public key to the client
- decrypt the HTTP message encrypted by the client with the help of the public key
- It was used to create the certificate signing request
- The private key may be stored in its own file or alternately in the same file as the certificate
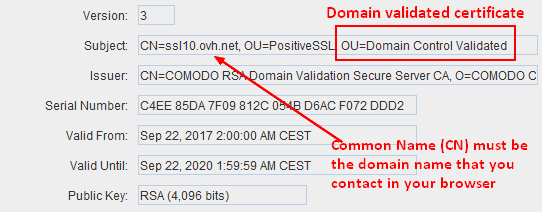
- A server domain validated certificate.
- It's a public entity and can be shared
- It should be issued (signed) by a trusted CA
- It is sent to every client that connects to the server in order to verify the server identity
- The size should be at minimum 2048 1)
- It must present the DNS name of the server in the Subject Alternative Name extension of the certificate. 2)
- It must have a validity period of 398 days or fewer 3)
- It must have the usage
For test purpose or for internal use you can be your own CA and self signed your certificate
Configuration
Once you got the signed certificate and the private key, you can configure your server:
For HTTP server:
- Nginx: Nginx - Https configuration
For a Net Server, you need to enable SNI if you want to show more than one certificate.
How to see the server certificate in the browser ?
You can see the certificate of the web site in the browser
What happens when the certificate is bad ?
Example (when the certificate is open with portecle)
If you access this website with the above certificate, you got a warning (Example below in firefox)