What are Host Keys?
About
Host keys are a key pairs for a host.
Each host can have one host key for each algorithm.
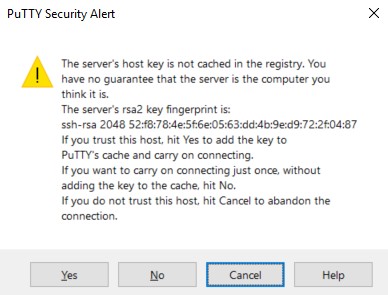
You should get an SSH host key fingerprint along with your credentials from a server administrator in order to prevent man-in-the-middle attacks.
Management
Create
The host keys are usually automatically generated when an SSH server is installed but you can recreate them on the server with keygen
ssh-keygen -l -f /etc/ssh/ssh_host_rsa_key
2048 0d:f4:2e:7b:be:e1:4c:0b:06:52:2b:4d:a4:51:1f:74 /etc/ssh/ssh_host_rsa_key.pub (RSA)
- Others
ssh-keygen -l -f /etc/ssh/ssh_host_dsa_key
ssh-keygen -l -f /etc/ssh/ssh_host_ecdsa_key
Location
Client
On the client to trust the host, you would need to add it in the known_hosts file
Server
On the server: Host keys are stored in the /etc/ssh/ directory.
Key Pair
The host keys are almost always stored in the following files:
/etc/ssh/ssh_host_dsa_key
/etc/ssh/ssh_host_ecdsa_key
/etc/ssh/ssh_host_ed25519_key
/etc/ssh/ssh_host_rsa_key
Public
ls /etc/ssh/*.pub
/etc/ssh/ssh_host_dsa_key.pub
/etc/ssh/ssh_host_ecdsa_key.pub
/etc/ssh/ssh_host_ed25519_key.pub
/etc/ssh/ssh_host_rsa_key.pub
cat /etc/ssh/ssh_host_rsa_key.pub
ssh-rsa AAAAB3NzaC1yc2EAAAADAQABAAABAQDwnFlKBk9t/pfd7vQGBrk+JNghDFJRa7G0rLrIoXUTtxconS7qZsZyTfEeh+l2cowWpKxpf03KyxouT7B3IdNjwXWHNKloQcE/8FYLhlcVw+Aicji5oUMdTfTberzCluYIyz4PUwE8rmgNejQbVLhl+lOfoacPMUJ4P6ahQ71WFTmFTEZ+CFnAmHeqtG7scl53DkICnXPkZ+57ymh1WM9h0kYFxVcZBXg7BOZpI/wrXkuWRXU6wpYHS481q/pjJTiLXZGIQhcXg1/inOCMgC1B9W92Rq/aviknWSS98/xQi2JbduG7Jw9Dn523Rs3nutUAQ6CMK7owjVtnvb54Bs1B root@buildbot-bbiwebhosting-builder-wheezy-amd64
Format
Fingerprint
The fingerpint of a public key consists of a hash (SHA256, MD5) of the public key. This is the same data that is base64 encoded to form the body of the public key file.
See The Secure Shell (SSH) Public Key File Format