Network - TLS
About
TLS is a cryptographic protocol and the successor to SSL, and is described in the RFC 2246 standard.
The protocol name was changed from SSL to TLS when it became a standard.
TLS is a protocol that helps provide privacy between communicating applications. When a server and client communicate, TLS ensures that no third party can overhear or tamper with any messages.
TLS is
- an option of a TCP connection
- may be used to secure UDP datagram (Rfc 6347 - Datagram Transport Layer Security Version (DTLS protocol) 1.2)
It secures the traffic from the beginning of the connection. If you want to secure the traffic in the middle of a plain text connection, you should use StartTLS
Version
| Externally | Internally |
|---|---|
| SSL 2.0 | SSL 2.0 |
| SSL 3.0 | SSL 3.0 |
| TLS 1.0 | SSL 3.1 |
| TLS 1.1 | SSL 3.2 |
| TLS 1.2 | SSL 3.3 |
Management
Handshake / Procedure
See SSL - Handshake (Negociation)
Installation
For SSL/TLS negotiation (handshake) to take place, the system administrator must prepare the minimum of 2 files:
- and Certificate.
See
Firefox:
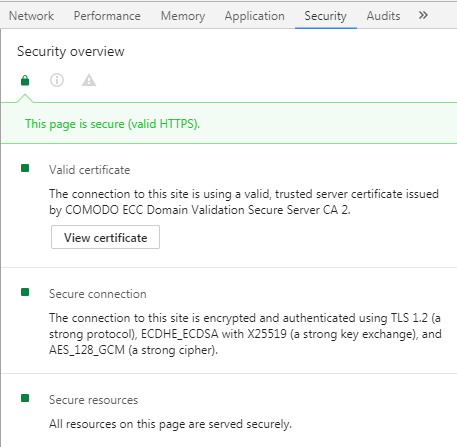
Chrome dev tool:
Check / Validate
https://www.ssllabs.com/ssltest/analyze.html
Documentation / Reference
-
- rfc5246 - The Transport Layer Security (TLS) Protocol Version 1.2