About
DomainKeys Identified Mail (DKIM) is a method:
- to sign digitally outgoing email,
- in order to authenticate a person, role, or organization
- allowing them to claim some responsibility for the message.
The signature associates:
- to an email message,
Usage
Because the DKIM process signs digitally all messages send, the receiving end can:
- authenticate the sender (not spam or phishing)
- verify that the message was not modified.
How it works
- The sender's mail server signs outgoing email with a private key.
- The receiver verifies the signature with the the public key that is made available in a DKIM DNS record.
Steps to set up DKIM
Generate a Private / Public Key Pair
As the first step, you should generate a key pair for your domain.
If you use an email provider, the key is provided by them.
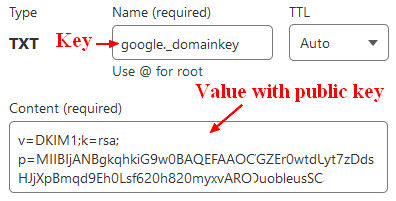
Create a DKIM DNS Record
A DNS record should create with:
- a DNS key
- that contains as value, the public key
Email servers can use this key to verify your messages' DKIM signatures.
Example for Google as email provider:
DKIM DNS Key
The DNS Key has the following structure:
selector._domainkey.domain
where selector permits to have several dkim signatory. See the selector section for more information
The domain is the DNS domain and is known as signing domain identifier (sdid) in the DKIM jargon.
Example:
my-provider._domainkey.my-domain.com
DKIM DNS Value
Example:
v=DKIM1;
k=rsa;
p=MIGfMA0GCSqGSIb3DQEBAQUAA4GNADCBiQKBgQDQUtHxTD63yxwq5fmjJ3RtXw2NP5/QEiSq3Xx85faTHnnj3/PA/igwWaueDsoeUuZOpkL74gDNGWBoQPecRaFrAXdPoEKGDYNBeMXzIkWQOth9Oaq4N+38LV08Ui86so8B2BhcvgXiqpACsrPur0hbDQWI183tZve7MKMPs3KPIQIDAQAB
where:
- k is the public key implementation (in this case: RSA)
- p is the public key
Enable DKIM and control the DKIM signature header
A DKIM filter is the filter application or client that adds the DKIM signature to all outgoing messages.
After enabling DKIM processing:
- the signature is added as in the DKIM-Signature header field
- the filter is added as in the DKIM-Filter header field
For example:
DKIM-Filter: OpenDKIM Filter v2.11.0 server01.bytle.net 3E16E1FBE8
DKIM-Signature: v=1; a=rsa-sha256; c=relaxed/relaxed; d=bytle.net;
s=dkimSelector; t=1591988898;
bh=WBggpZrfs7F0OzQkyE7LiZPHyfFFhl7N4CNav2f5YVw=;
h=Date:To:Subject:From:From;
b=ByN4Iw4U9RP8bzaPK0n3HJbFlvI60ett+V9pkoli+UNtdAcSdq/ANc3hL71PzjrT4
3yyTjK3MC5e2f/k+BAnIaAgnradAK/1CbMF4vMZVD6WoVIx7KTZlfWsW39Ir8PhqYQ
4TKvPpDUx8ToxUz1gwQlxJoExYW3McXJ2WdvUAf8=
where:
- a is the algorithm used to generate the signature. Mostly rsa-sha256, ie a RSA signature hashed by the sha256 algorithm)
- s is the dkim selector that you find in the domain record
- d is the domain known as sdid
- i is the Agent or User Identifier (AUID)
- t is the Signature Timestamp
- b is the signature (ie the output if the signature algorithm)
- h is the header fields used as input of the signature algorithm
- Example of values: h=Date:From:Reply-To:To:Cc:In-Reply-To:References:Subject:List-ID:
- c specifies the canonicalization algorithms for the headers and body (default is simple/simple). It manages how the email can be modified in transit while preserving the signature:
- simple tolerates almost no email modification in transit
- relaxed tolerates common modifications such as whitespace replacement and header field line rewrapping.
Metadata
This section talks about the metadata that are included in the DKIM-Signature value.
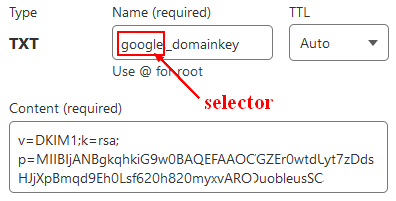
Selector
The selector permits selecting the DNS record that contains the public key. It has generally the value of your mail provider that will sign your email.
The DKIM selector:
- is specified as an attribute of the DKIM-signature header field (the s key) in the emails send.
- permit multiple public keys (under the same organization's domain name).
Example with an entry for google:
Signing Domain Identifier (SDID)
The sdid 1) is the domain site where the public key can be found. In the DKIM Signature header, you can find it in the d property:
Example:
DKIM-Signature: v=1; a=rsa-sha256; c=relaxed/relaxed; d=bytle.net;
s=dkimSelector; t=1591988898; ...
Agent or User Identifier (AUID)
The AUID 2) is an optional value that identifies the user agent that has signed the message.
You can find its value in the signature on the i property.
Example:
DKIM-Signature: v=1; a=rsa-sha256; c=simple/simple; d=example.com; [email protected];
s=selector;
The value is an email value.
Example of values:
- Mailchimp: [email protected]
The default value is
- an empty local part
- followed by @
- followed by the signing_domain_identifier_sdid
How to lookup DKIM record ?
You can lookup the dkim record.
Example with Nslookup
# nslookup -type=TXT selector._domainkey.sdid
nslookup -type=TXT google._domainkey.datacadamia.com
Non-authoritative answer:
google._domainkey.datacadamia.com text =
"v=DKIM1; k=rsa; p=MIIBIjANBgkqhkiG9w0BAQEFAAOCAQ8AMIIBCgKCAQEAkGtLDG3wTcwJIuWDiKLXIAB1VmIRKbt0G6RamA6I+vbJf9HmTcKnVtcGsTl5fNnOdBCpyZXn6Kq+swwmQXH91D0yjStlExS2hr56qIEcCm2lecKq98PdQtQA0BKE0bEna1xryiwlNCKtH2ZqipIwFHmZgTV3WPOkjqwNQxoj4m93EXZktfslUnP88v9ArHOZM"
Alignment
DKIM alignment is a check that compares:
- the domain of the DKIM signature (the field d=)
- to the domain of the author address (the From: header)
Examples of checks and their results:
| Author (From: header) | DKIM domain | Strict alignment | Relaxed alignment |
|---|---|---|---|
| [email protected] | foo.com | Pass | Pass |
| [email protected] | foo.com | Fail | Pass |
| [email protected] | foo.dev | Fail | Fail |
You can set the type of checks with the adkim attribute of the DMARC record with:
- a s for strict
- a r for relaxed
Library
Below are libraries or software that can help you set up a DKIM process:
- Java apache: apache-jdkim-library
- Vertx: Mail client library