About
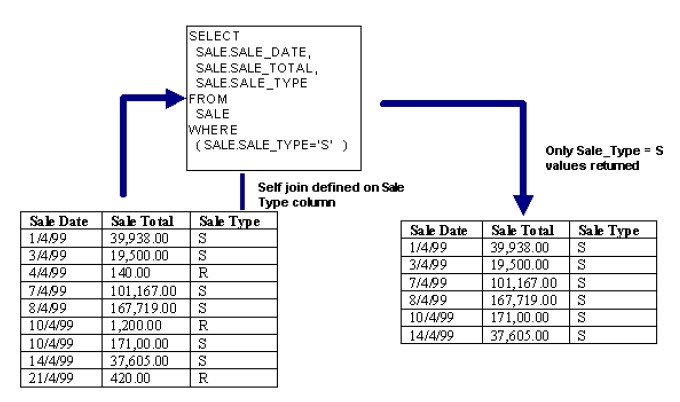
A self restricting join is not really a join at all, but a self restriction on a single table. You can use a self restricting join to restrict the results returned by a table values using a fixed value.
Example
Properties
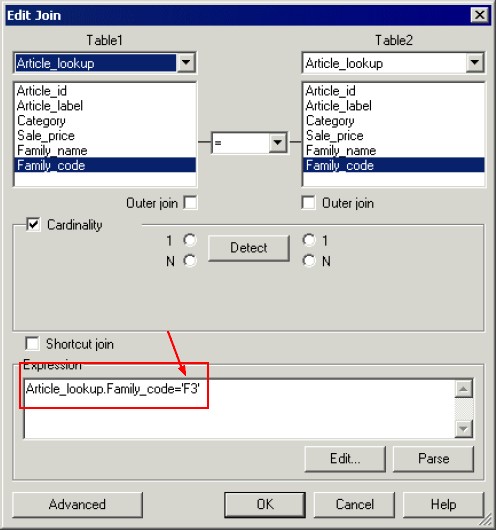
For example, if you want to restrict the returned values from the Family_code column to 'F3', you replace Article_lookup.Family_code (which come from table2) after the = sign with 'F3' as shown below:
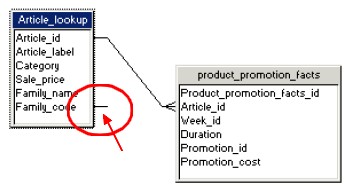
In a structure pane
The self restricting join appears as a short line displayed against the column on which the self restricting join is defined.